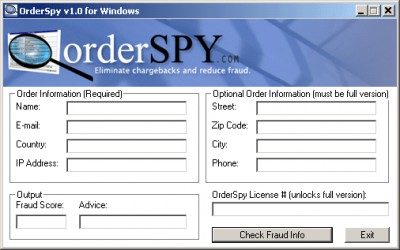
OrderSpy 1.0
 OrderSpy automatically analyses over 25 bits of information about online orders to determine if the order is fraudulent.
OrderSpy automatically analyses over 25 bits of information about online orders to determine if the order is fraudulent.
|
OrderSpy automatically analyses over 25 bits of information about online orders to determine if the order is fraudulent.
Orders may be screened for fraud before or after they are processed by the merchant. Order information may also be entered in by the merchant manually. OrderSpy is easy to setup and install, available in Perl, CGI, PHP, and Python and manual-mode is compatible with any web browser.
OrderSpy may be configured to give a fraud score, or to accept, reject transactions with a given fraud threshold, log all suspicious orders, or have the merchant manually review the order before or after it submitted to the merchant gateway or to the merchant E-mail address.
This software will reduce fraud rates on your website or for your offline business by catching chargebacks before they happen. No programming knowledge is required.
OrderSpy features include the folowing: evaluates the risk of accepting an order and gives advice; searches databases of known fraudulent orders and IP addresses; better than a human in many cases at detecting fraudulent orders; usually takes less than one second to process order information; configurable to send you fraud alert E-mails, log transactions, or halt the order process if order is fraudulent.
tags![]() the merchant fraudulent orders the order merchant manually order information
the merchant fraudulent orders the order merchant manually order information
Download OrderSpy 1.0
Purchase: ![]() Buy OrderSpy 1.0
Buy OrderSpy 1.0
Similar software
 OrderSpy 1.0
OrderSpy 1.0
OrderSpy.com
OrderSpy automatically analyses over 25 bits of information about online orders to determine if the order is fraudulent.
 ShopSuxess 4 SR3
ShopSuxess 4 SR3
Exody
ShopSuxess helps you to precisely analyze strengths and weaknesses of online shops and provides valuable suggestions to improve the shop and its
"Return on Internet.
 GralicWrap for Windows 1.06
GralicWrap for Windows 1.06
GralicWrap.com
GralicWrap is a very large and constantly-updating database and protection program against fraudulent sites on the web.
 eOrdering Professional 4.1.2
eOrdering Professional 4.1.2
LAJ Design
eOrdering Professional allows small and large businesses, photographers, and artists to put their products online and take orders online.
 eOrdering Gold 4.1.2
eOrdering Gold 4.1.2
LAJ Design
eOrdering Gold - small businesses, photographers, and artists put your products online and take orders over the web.
 Software and Order Administration 3.8.0.3
Software and Order Administration 3.8.0.3
SoftRM
Software and Order Administration provide a toolkit for shareware authors, software companies, software resellers to administrate software and orders, with Software and Order Administration you can administrate your development and your orders easily , keep in touch with your customers in time.
 Microsoft Phishing Filter Add-in for MSN Search Toolbar 3.0.4702.0
Microsoft Phishing Filter Add-in for MSN Search Toolbar 3.0.4702.0
Microsoft
Phishing (pronounced "Fishing") is one of the fastest growing threats on the Internet and a form of identity theft.
 KeyFour Restaurant 6.0
KeyFour Restaurant 6.0
888bid.com
KeyFour Restaurant is a restaurant management software application, which used by restaurants to enter orders for dine-in and takeout, processing orders, printing bills and reservation etc.
![]() Time Tracker Employee Scheduling Software 5.1.509
Time Tracker Employee Scheduling Software 5.1.509
Asgard Systems Incorporated
Time Tracker Employee Scheduling Software automates and analyses the scheduling process.
 SafeShopper 1.2
SafeShopper 1.2
K.soft
Is your credit card really safe after you have placed an order online, or is your information only a password guess away from a hacker? You may be surprised how many online stores leave critical backdoors open on their computers.