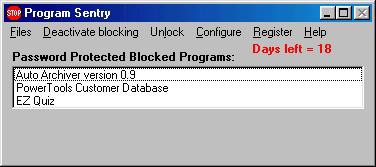
Program Sentry 2.1.0
 Provides access control and usage management.
Provides access control and usage management.
|
Provides access control and usage management. When installed, it allows you to either create a list of blocked programs or a list of allowed programs. In the blocked programs mode, any program on the list is blocked. In the allowed program mode, any program NOT on the list is blocked. Which mode you choose to use depends on whether you have a few programs you want to block (in which case you would use the blocked program mode), or you have a few programs you want to allow people to use (in which case you would use the allowed program mode).
In both modes, you can assign optional passwords to the programs on the list. In blocked program mode, if no password is assigned to a program, it cannot be individually unblocked. If a password is assigned to a blocked program, it can be unblocked using the password. In the allowed program mode, if no password is assigned to the program, it is never blocked. If a password is assigned to the program, it is blocked until someone enters the password for that program. passwords are useful if several people use the computer, and you want each to be allowed to use different programs. You can give each person the passwords to the programs they are allowed to use.
An administrator password is required to add or remove programs from the lists or change their passwords. This provides the person who installs Program Sentry with the ability to completely control the use of a computer. All blocking can be temporarily turned off using supervisor level password. This password cannot be used to add programs to (or remove programs from) the program lists.
This program is most useful in a business setting, where the supervisor needs the ability to control who can do what on each company computer. It can also be useful in a family setting, however, to give parents control of the computer to block children from using certain programs.
tags![]() program mode blocked program programs you you want allowed program the allowed use the the program the list you can the programs the password remove programs
program mode blocked program programs you you want allowed program the allowed use the the program the list you can the programs the password remove programs
Download Program Sentry 2.1.0
Purchase: ![]() Buy Program Sentry 2.1.0
Buy Program Sentry 2.1.0
Similar software
 Program Sentry 2.1.0
Program Sentry 2.1.0
Leithauser Research
Provides access control and usage management.
 Program Selector Pro 98/ME 4.3
Program Selector Pro 98/ME 4.3
Leithauser Research
Program Selector Pro 98/ME is a computer security program that provides access control and usage management.
 Program Selector Pro 2000/XP 4.3
Program Selector Pro 2000/XP 4.3
Leithauser Research
Program Selector Pro 2000/XP is a computer security software that provides access control and usage management.
 Web Padlock 3.2
Web Padlock 3.2
Leithauser Research
Web Padlock is a program that provides access control and usage management over your computer's Web browser.
 BrowseControl 5.2
BrowseControl 5.2
Codework Solutions (P) Ltd.
BrowseControl is designed as the perfect solution for controlling internet and application usage in the network.
 Installed Programs Finder 1.0
Installed Programs Finder 1.0
CaldSoft
With Installed Programs Finder you will be able to identify every program installed on your computer.
 AOL Internet Access Controls 2.0 beta 5
AOL Internet Access Controls 2.0 beta 5
AOL
Internet Access Controls ("IAC") are designed to help give parents more control over the online content available to their kids.
 UninstallDummy! 1.2
UninstallDummy! 1.2
ksoft
Do you have programs listed in your Control Panel's Add/Remove Programs list that you just can't seem to remove?
UninstallDummy! is an easy solution to highlight, uninstall, and remove phantom program entries in your Add/Remove Programs list.
 AntiFirewall 1.10
AntiFirewall 1.10
iNetPrivacy Software
AntiFirewall is a firewall terminator and anonymizer which allows you to connect to newsgroups, FTP, ICQ, IRC and e-mail although you are behind a firewall blocking access to these programs/ protocols.
 SentryPC 2.30
SentryPC 2.30
Spytech Software
With SentryPC you can restrict and monitor your computer allowing access to what you want when you want for all users!
Specify the hours, the days, and total usage time for virtually every aspect of your computer including specific programs, websites, and basic computer and Internet usage! SentryPC can also monitor and record all keystrokes, website visits, windows interacted with, chat conversations, and even applications used.