Personal Firewall PF 2.5.0.4
 Stolen files, Trojan horse, distributed attacks, identity thiefs remote dump or remote system crash … Those classic attacks are not isolated nor rare plus there are those we don't know yet … Hackers are not anymore extremely skilled group of people, you can see now novice copying threats without difficulties from others on Internet.
Stolen files, Trojan horse, distributed attacks, identity thiefs remote dump or remote system crash … Those classic attacks are not isolated nor rare plus there are those we don't know yet … Hackers are not anymore extremely skilled group of people, you can see now novice copying threats without difficulties from others on Internet.
|
Stolen files, Trojan horse, distributed attacks, identity thiefs remote dump or remote system crash … Those classic attacks are not isolated nor rare plus there are those we don't know yet … Hackers are not anymore extremely skilled group of people, you can see now novice copying threats without difficulties from others on Internet.
They occur everyday on your machine mainly laptops without even noticing sometimes. Your sales force are on the road, your branch offices are 24/7 DSL connected, mobile workers are working from home with permanent cable connections making the attacks easier.
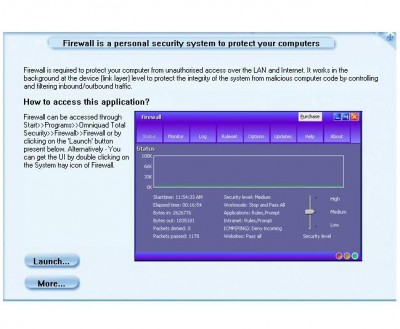
You don't need any technical security background or skills to install and configure. Personal Firewall will learn your privacy rules based on your browsing habits and used types of activtities. No useless popup: TheGreenBow protects you on the back stage but you can have access to some statistics or configuration if you like via the tray bar icon.
Distributed Management is available in Personal Firewall. Security can be managed without changing behaviors of users, without users even noticing !! If distributed management is activated, the Personal Firewall will fetch Security Policies onto the Central Policy Server and will report 360° reporting logs back to the Server (virus alert, traffic monitoring, policy violation). Integration with existing network management with our https/Syslog network interface.
Limitations
tags![]() personal firewall firewall will distributed management even noticing you can are not
personal firewall firewall will distributed management even noticing you can are not
Download Personal Firewall PF 2.5.0.4
![]() Download Personal Firewall PF 2.5.0.4
Download Personal Firewall PF 2.5.0.4
Purchase: ![]() Buy Personal Firewall PF 2.5.0.4
Buy Personal Firewall PF 2.5.0.4
Similar software
 Personal Firewall PF 2.5.0.4
Personal Firewall PF 2.5.0.4
Sistech SA
Stolen files, Trojan horse, distributed attacks, identity thiefs remote dump or remote system crash … Those classic attacks are not isolated nor rare plus there are those we don't know yet … Hackers are not anymore extremely skilled group of people, you can see now novice copying threats without difficulties from others on Internet.
 Trojan Remover 6.8.2
Trojan Remover 6.8.2
Simply Super Software
Trojan Remover was written to aid in the removal of Trojan Horses and Internet Worms when standard anti-virus software has either failed to detect the problem or is unable to effectively eliminate it.
 DebugView 4.64
DebugView 4.64
Mark Russinovich
DebugView is a program which helps you monitor debug output on your local system, or any computer on the network that you can reach via TCP/IP.
 Remote Access 2.0 2.0.0
Remote Access 2.0 2.0.0
Remote Access
Remote Access 2.
 Beyond Remote 2.5.1.450
Beyond Remote 2.5.1.450
Data Apples Corporation
Beyond Remote will allow you to view remote computers live and also transfer files and chat with the remote person.
 Remote Batch Copy 7.7.0
Remote Batch Copy 7.7.0
Morning Glory Technologies
Remote Batch Copy is an application that allows you copy multiple files to multiple remote directories.
 Remote Control Lan 2.7
Remote Control Lan 2.7
IntelliNavigator
Remote Control Lan is a useful remote control solution designed for your LAN.
 Look 'n' Stop Firewall 2.05
Look 'n' Stop Firewall 2.05
Soft4Ever
Look 'n' Stop provides a permanent and highly secured protection against Internet hacker attacks.
 RDM+ 3.2.2
RDM+ 3.2.2
ZZZ Software
Remote Desktop for Mobiles it is easy-to-use, reliable and secure remote control software which will allow you to work on the remote home or office computer from your mobile phone.
 BlackICE PC Protection 3.6cqc
BlackICE PC Protection 3.6cqc
Network ICE
BlackICE teams a personal firewall with an advanced intrusion detection system to constantly watch your Internet connection for suspicious behavior.